Stateful Packet Inspection is a dynamic packet filtering technique for firewalls that, in contrast to static filtering techniques, includes the state of a data connection in the inspection of packets. It detects active TCP sessions and can allow or block data packets based on the session state. SPI provides higher security for firewall inspection and reduces the number of rules that need to be defined.
Welcome, curious readers, to a journey through the realms of network security! In our digital age, where data flows ceaselessly across vast networks, safeguarding information has become paramount. As we navigate the vast landscape of firewalls and their intricate workings, today’s spotlight shines on an essential guardian: Stateful Packet Inspection (SPI).
Get ready to unlock the secrets behind this formidable technology as we delve into its inner workings, understand its significance, and explore how it fortifies our digital frontiers. Brace yourself for a captivating exploration of the dynamic world of network security and the prowess of Stateful Packet Inspection!
Contents
- What is Stateful Packet Inspection (SPI)?
- How Stateful Packet Inspection Works
- Stateful Packet Inspection in Practice
- Limitations and Considerations
- Best Practices for Implementing Stateful Packet Inspection
- Stateful Packet Inspection Related Terms
- Frequently Asked Questions
- How does Stateful Packet Inspection differ from Stateless Packet Filtering?
- Can Stateful Packet Inspection block specific applications or protocols?
- Does Stateful Packet Inspection affect network performance?
- Can Stateful Packet Inspection prevent all types of network attacks?
- Is Stateful Packet Inspection effective against encrypted traffic?
- Does Stateful Packet Inspection replace the need for antivirus software?
- Can Stateful Packet Inspection detect and block malicious content within packets?
- What are the challenges of implementing Stateful Packet Inspection in large-scale networks?
- Can sophisticated attackers bypass Stateful Packet Inspection?
- Is Stateful Packet Inspection suitable for both small and enterprise-level networks?
- Conclusion
What is Stateful Packet Inspection (SPI)?
Stateful Packet Inspection (SPI) is a vital component of modern network security systems, acting as a vigilant gatekeeper that scrutinizes incoming and outgoing network traffic. It goes beyond the capabilities of traditional firewalls by examining not just individual packets but also the context and state of the network connections.
At its core, SPI monitors the flow of data packets in a network, meticulously inspecting their content, header information, and the associated connection state. By maintaining a record of previous packets exchanged within a connection, SPI can make informed decisions about the legitimacy of incoming traffic.
The importance of SPI in network security cannot be overstated. Here are a few key reasons why it has become an indispensable tool:
- Enhanced Security: SPI provides a higher level of security by intelligently analyzing packets and ensuring that they adhere to established security policies. By actively monitoring the state of connections, SPI can detect and block suspicious or unauthorized activities, protecting networks from various types of attacks.
- Contextual Awareness: Unlike basic packet filtering, SPI is aware of the context and state of network connections. It keeps track of the source, destination IP addresses, port numbers, and other relevant information to determine whether a packet is part of an established connection or a potential threat. This context-driven approach enables more precise identification of malicious activities.
- Granular Control: SPI allows network administrators to define and enforce specific security policies based on various criteria, such as source/destination IP addresses, port numbers, or application protocols. This level of granular control empowers organizations to tailor their security measures according to their unique requirements, ensuring efficient traffic management while mitigating potential risks.
- Prevention of Network Attacks: SPI acts as a first line of defense against a wide range of network attacks, including intrusion attempts, denial-of-service (DoS) attacks, and malware infections. By inspecting packets in real-time and comparing them against known attack signatures or behavioral patterns, SPI can identify and block potentially harmful traffic, preventing successful breaches.
- Improved Performance: Although SPI involves more intensive processing compared to basic packet filtering, modern hardware and software implementations have significantly reduced its impact on network performance. By intelligently filtering and processing only relevant traffic, SPI helps optimize network resources and maintain high-performance levels while ensuring robust security.
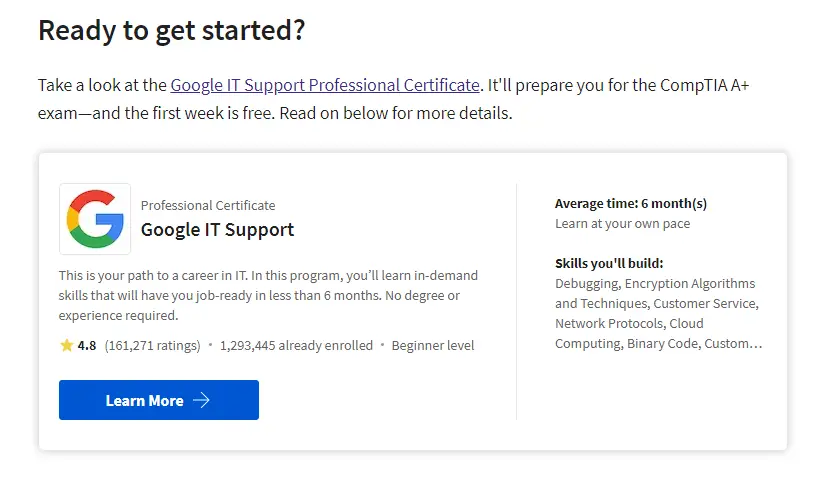
|Looking for a Course to prepare for your CompTIA A+? Check out this course on Coursera.
In today’s increasingly interconnected and vulnerable digital landscape, Stateful Packet Inspection stands as a formidable defense mechanism, providing crucial protection against threats and allowing organizations to maintain the integrity and confidentiality of their networks.
How Stateful Packet Inspection Works
Stateful Packet Inspection (SPI) operates by intelligently analyzing the content and context of network packets to enforce security policies and protect against potential threats. To understand how SPI works, let’s delve into its functioning, the distinction between stateful and stateless firewalls, and the role of packet filtering and connection state tables.
Packet Filtering
Packet filtering is a fundamental technique used by firewalls to control network traffic based on predefined rules. It involves inspecting individual packets and making decisions about whether to allow or block them based on specific criteria, such as source/destination IP addresses, port numbers, or protocols.
Stateful vs. Stateless Firewalls
| Criteria | Stateless Firewall | Stateful Firewall |
|---|---|---|
| Packet Evaluation | Analyzes individual packets | Analyzes packets within connection state |
| Connection Awareness | Lacks awareness of connection state | Maintains information about connection state |
| Contextual Analysis | Does not consider packet sequence or context | Considers packet sequence and context |
| Rule Complexity | Rules are based on packet header information only | Rules can consider packet header, payload, and connection state |
| Security Effectiveness | Provides basic security measures | Offers enhanced security against advanced threats |
| Performance Impact | Lighter processing, lower resource consumption | Requires more processing power and resources |
| Granularity of Control | Limited granularity in rule enforcement | Allows for granular control based on connection state and packet contents |
| Network Visibility | Provides limited visibility into network traffic | Offers deeper insights into network traffic and behavior |
| Intrusion Detection | Limited capabilities for intrusion detection | Enables more effective intrusion detection and prevention |
| Scalability | Generally more scalable | May have limitations in handling large-scale networks |
| Examples | Traditional packet filtering firewalls | Stateful Packet Inspection (SPI) firewalls |
Stateless firewalls, also known as packet filtering firewalls, make decisions on a packet-by-packet basis without considering the context or connection state. They evaluate each packet independently and do not maintain any information about past packets. While stateless firewalls offer basic security, they lack the ability to track and analyze packet sequences, making them less effective against advanced threats.
On the other hand, stateful firewalls, like SPI, go beyond simple packet filtering. They maintain information about the state of network connections by creating and managing connection state tables. By tracking the flow of packets within a connection, stateful firewalls can make more informed decisions and provide enhanced security.
Functioning of Stateful Packet Inspection
Stateful Packet Inspection combines packet filtering with the maintenance of connection state tables.
Packet Header and Payload Examination
SPI inspects both the header and payload of network packets. The header contains vital information like source/destination IP addresses, port numbers, and protocol details. The payload contains the actual data being transmitted.
Maintaining Connection State Tables
SPI creates and maintains connection state tables to keep track of the state of network connections. These tables store information about established connections, including IP addresses, port numbers, sequence numbers, and more. The state table enables SPI to identify subsequent packets that belong to the same connection.
Packet Decision Making
When a packet arrives, SPI compares its characteristics against the defined security policies and rules. It considers factors such as the packet’s source and destination addresses, port numbers, and the corresponding connection state. Based on this analysis, SPI determines whether to allow or block the packet.
Dynamic Rule Modification
SPI can dynamically modify its rules based on the current connection state and security requirements. For example, it may allow certain types of traffic during an established connection but block them during the connection establishment phase.
By employing these mechanisms, SPI provides a more comprehensive and context-aware approach to network security, allowing it to detect anomalies, prevent unauthorized access, and mitigate potential threats effectively.
Stateful Packet Inspection plays a crucial role in securing modern networks by combining the strengths of packet filtering and connection state tracking. Its ability to maintain and analyze connection state tables enables more sophisticated threat detection, precise rule enforcement, and enhanced network protection.
Stateful Packet Inspection in Practice
Stateful Packet Inspection (SPI) finds practical implementation in various areas of network security, including firewalls, intrusion detection/prevention systems (IDS/IPS), and virtual private networks (VPNs). Let’s explore how SPI is utilized in each of these domains.
Implementation in Firewalls
Firewalls are the primary line of defense in network security, and SPI plays a critical role in their operation. SPI-enabled firewalls analyze incoming and outgoing network traffic, examining packet headers, payload contents, and connection states.
By comparing this information against predefined security policies, SPI determines whether to permit or block packets. SPI-enhanced firewalls provide more robust protection than traditional packet filtering firewalls by considering the context of network connections and maintaining connection state tables.
Application in Intrusion Detection/Prevention Systems (IDS/IPS)
Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) monitor network traffic for signs of unauthorized access, malicious activities, or suspicious behavior. SPI technology strengthens the capabilities of IDS/IPS by allowing them to perform in-depth analysis of packets and connection states.
SPI helps detect and flag potential intrusions by examining patterns, identifying anomalies, and comparing network traffic against known attack signatures. In IPS, SPI can go a step further by actively blocking malicious packets or connections, preventing successful intrusions.
Use in Virtual Private Networks (VPNs)
VPNs establish secure and encrypted connections over public networks, enabling remote users to access private networks and resources securely. SPI plays a vital role in VPNs by ensuring the integrity and confidentiality of data transmitted through encrypted tunnels.
SPI-enabled VPNs verify packet headers, inspect payload contents, and maintain connection state tables to guarantee that only legitimate VPN traffic is allowed. By examining VPN packets, SPI can prevent unauthorized access attempts, protect against VPN tunnel hijacking, and enforce security policies specific to VPN connections.
In all these applications, SPI acts as an intelligent and dynamic security mechanism, providing comprehensive network traffic inspection and analysis. By considering packet content, header information, and connection state, SPI enables efficient identification of potential threats, effective rule enforcement, and robust protection of networks and sensitive data.
It’s worth noting that the implementation and capabilities of SPI may vary across different network security devices and systems. The level of customization, rule management, and performance optimizations can differ based on specific hardware, software, and security requirements.
Nonetheless, the underlying principle of SPI remains consistent – it combines packet filtering with connection state tracking to deliver advanced network security solutions.
Limitations and Considerations
While Stateful Packet Inspection (SPI) is a powerful network security technology, it is important to be aware of its limitations and consider certain factors when implementing and using it. Let’s explore some key considerations:
Resource Consumption
SPI involves more intensive processing compared to basic packet filtering, which can impact network performance and consume system resources. Inspecting and analyzing packet headers, payload contents, and maintaining connection state tables require computational power and memory. It is crucial to assess the hardware capabilities and network requirements to ensure that SPI does not adversely affect the overall network performance.
Complex Rule Configuration
SPI-enabled systems often require more intricate rule configuration compared to basic packet filtering. Defining and managing security policies and rule sets can become complex, especially in large-scale networks. Careful planning, documentation, and regular updates are essential to maintain a robust security posture. Organizations should also consider investing in user-friendly management interfaces or tools to simplify rule configuration and monitoring.
Encryption and Encapsulated Traffic
While SPI can analyze packet headers and some aspects of payload contents, it faces limitations when dealing with encrypted or encapsulated traffic. Encrypted traffic, such as HTTPS, obscures the payload contents, making it difficult for SPI to inspect the data. Similarly, encapsulated traffic, like VPN tunnels, hides the original packet structure, posing challenges for SPI to examine the encapsulated data. In such cases, additional security measures, like deep packet inspection (DPI) or dedicated encryption/decryption mechanisms, may be required to complement SPI.
Evasion Techniques
Sophisticated attackers may employ evasion techniques to bypass SPI. They may fragment packets, modify packet headers, or use covert channels to hide malicious activities from SPI inspection. These evasion techniques can exploit vulnerabilities in SPI implementations and compromise network security. Regular updates of SPI software/firmware, staying informed about emerging evasion techniques, and employing complementary security measures can help mitigate these risks.
Scalability and Performance
In highly complex and high-traffic environments, the scalability and performance of SPI systems become crucial. As network size and traffic volume increase, the ability of SPI to handle the load effectively and maintain optimal performance becomes essential. It is vital to assess the scalability features and performance benchmarks of SPI solutions to ensure they meet the demands of the network.
Best Practices for Implementing Stateful Packet Inspection
When implementing Stateful Packet Inspection (SPI) for network security, several best practices can help maximize its effectiveness and ensure a strong security posture. Consider the following recommendations:
Regular Updates and Patch Management
Stay vigilant about keeping SPI software/firmware up to date. Regularly apply security patches and updates provided by the vendor to address any known vulnerabilities. This helps protect against emerging threats and ensures that the SPI system benefits from the latest security enhancements.
Rule Optimization and Maintenance
Regularly review and optimize the security rules and policies defined within the SPI system. Remove unnecessary rules, consolidate overlapping rules, and ensure that the rule set aligns with the organization’s specific security requirements. Periodic reviews help improve performance, reduce rule conflicts, and maintain an efficient and effective security posture.
Integration with Other Security Measures
SPI should not be implemented in isolation. Integrate it with other security measures, such as intrusion detection/prevention systems (IDS/IPS), antivirus software, and security information and event management (SIEM) solutions. This integration strengthens overall network security, enhances threat detection capabilities, and provides a comprehensive defense against a wide range of attacks.
Monitoring and Logging
Implement robust monitoring and logging mechanisms to capture and analyze SPI activities. Monitor network traffic, examine logs, and set up alerts for suspicious or anomalous behavior. Monitoring and logging help detect potential threats, identify security gaps, and facilitate incident response and forensic investigations when necessary.
Security Audits and Assessments
Conduct regular security audits and assessments to evaluate the effectiveness of SPI implementation and identify potential weaknesses. Engage third-party security experts or conduct internal assessments to assess the configuration, performance, and overall security posture of the SPI system. These audits can uncover vulnerabilities, ensure compliance with industry standards, and provide valuable insights for improving security measures.
Employee Awareness and Training
Educate employees about SPI and its role in network security. Promote awareness of security best practices, such as avoiding suspicious websites, practicing strong password hygiene, and being cautious about opening email attachments or clicking on suspicious links. Well-informed employees can act as an additional layer of defense, complementing the effectiveness of SPI.
Stateful Packet Inspection Related Terms
Deep Packet Inspection (DPI)
Deep Packet Inspection is an advanced network analysis technique that goes beyond traditional packet inspection. It involves the comprehensive examination of the entire packet, including the payload contents, to gain deep insights into the network traffic.
DPI allows for the detection of specific application protocols, identification of malicious activities, and the ability to enforce more granular security policies.
Deep Packet Inspection Firewall
A Deep Packet Inspection (DPI) Firewall is a security device or software that combines traditional firewall functionality with the capabilities of deep packet inspection. It goes beyond basic packet filtering and examines the contents of packets at a granular level.
DPI firewalls can analyze packet payloads, inspect application-layer protocols, and identify specific traffic patterns or behaviors. This enables them to provide advanced threat detection, content filtering, intrusion prevention, and application-level visibility and control.
Stateless Packet Inspection
Stateless Packet Inspection refers to the process of inspecting network packets without considering the connection state. It focuses on examining individual packets based on predefined criteria, such as source/destination IP addresses, port numbers, or protocol types.
Stateless packet inspection is a basic form of packet filtering lacking the contextual understanding stateful inspection provides. While it can provide basic security measures, it may be less effective against sophisticated attacks that rely on exploiting connection states or analyzing packet sequences.
Frequently Asked Questions
How does Stateful Packet Inspection differ from Stateless Packet Filtering?
Stateful Packet Inspection (SPI) goes beyond basic packet filtering performed by stateless firewalls. While stateless packet filtering examines individual packets based on criteria like source/destination IP addresses and port numbers, SPI maintains connection state tables and considers the context of network connections. SPI analyzes packet sequences, inspects payload contents, and makes decisions based on the state of connections, providing more advanced security capabilities.
Can Stateful Packet Inspection block specific applications or protocols?
Yes, Stateful Packet Inspection can block specific applications or protocols. By inspecting packet contents and headers, SPI can identify specific applications or protocols and apply security policies to block or allow them. This granular control allows network administrators to enforce restrictions on certain applications or protocols based on security requirements or organizational policies.
Does Stateful Packet Inspection affect network performance?
Stateful Packet Inspection can have an impact on network performance, especially in high-traffic environments. The inspection and analysis of packets, maintenance of connection state tables, and deeper analysis of packet contents require additional processing power and resources. While modern hardware and software implementations have improved performance, organizations should consider SPI’s scalability and resource requirements to ensure optimal network performance.
Can Stateful Packet Inspection prevent all types of network attacks?
While Stateful Packet Inspection is a powerful security mechanism, it cannot prevent all types of network attacks. SPI is effective against various threats, including intrusion attempts, denial-of-service attacks, and unauthorized access attempts. However, sophisticated attacks using advanced evasion techniques or exploiting vulnerabilities in specific protocols may require additional security measures or specialized tools to complement SPI’s capabilities.
Is Stateful Packet Inspection effective against encrypted traffic?
Stateful Packet Inspection faces limitations when dealing with encrypted traffic. While SPI can analyze packet headers, it cannot inspect the contents of encrypted data. Encrypted traffic, such as HTTPS, obscures the payload contents, making it challenging for SPI to examine the data.
However, SPI can still analyze the packet headers, track connection states, and make decisions based on contextual information to enforce security policies for encrypted traffic. Additional security measures like deep packet inspection (DPI) may be required to inspect encrypted traffic thoroughly.
Does Stateful Packet Inspection replace the need for antivirus software?
No, Stateful Packet Inspection (SPI) does not replace the need for antivirus software. While SPI can provide network-level security by inspecting packets and maintaining connection state tables, antivirus software is specifically designed to detect and mitigate malware threats at the endpoint level.
Antivirus software scans files and programs on devices to identify and remove or quarantine malicious content. It is recommended to have a multi-layered security approach that combines SPI, antivirus software, and other security measures to provide comprehensive protection.
Can Stateful Packet Inspection detect and block malicious content within packets?
Stateful Packet Inspection has limited capabilities in detecting and blocking specific types of malicious content within packets. SPI primarily focuses on inspecting packet headers, maintaining connection state, and enforcing security policies based on contextual information.
While it can identify known attack signatures or patterns, its ability to detect and block specific malicious content within packets may be limited. Additional security measures like intrusion detection/prevention systems (IDS/IPS) and deep packet inspection (DPI) can be employed to enhance the detection and blocking of malicious content.
What are the challenges of implementing Stateful Packet Inspection in large-scale networks?
Implementing Stateful Packet Inspection (SPI) in large-scale networks poses several challenges. Some of these challenges include:
- Performance and scalability: SPI’s processing requirements and the maintenance of connection state tables can strain resources in large-scale networks, potentially impacting performance.
- Rule complexity and management: As network size grows, managing and optimizing security rules becomes more complex. Ensuring rule consistency, avoiding conflicts, and keeping up with changes in network architecture can be challenging.
- Network topology and traffic patterns: Large-scale networks often have complex topologies and diverse traffic patterns, which can complicate the identification of legitimate traffic and potential threats. Tuning SPI to accurately identify and handle such patterns can be challenging.
- Resource allocation: Allocating sufficient resources, such as processing power, memory, and bandwidth, to support SPI in large-scale networks is crucial. Inadequate resource allocation can lead to degraded performance or insufficient security coverage.
Can sophisticated attackers bypass Stateful Packet Inspection?
Stateful Packet Inspection can be bypassed or circumvented by sophisticated attackers who exploit vulnerabilities or use advanced evasion techniques. Attackers may fragment packets, modify packet headers, or use covert channels to evade SPI inspection.
They can also target weaknesses in the implementation or configuration of SPI systems. To mitigate these risks, regular updates of SPI software/firmware, staying informed about emerging evasion techniques, and employing complementary security measures are important.
Is Stateful Packet Inspection suitable for both small and enterprise-level networks?
Yes, Stateful Packet Inspection is suitable for both small and enterprise-level networks. SPI can be implemented in various network environments and scaled to meet the needs of different-sized networks. Whether it is a small office network or a large enterprise network, SPI offers enhanced security capabilities by considering packet contents, connection states, and applying contextual analysis.
However, it is important to consider the specific requirements, network architecture, and resource constraints when implementing SPI to ensure optimal performance and effectiveness.
Conclusion
In conclusion, Stateful Packet Inspection (SPI) serves as a vital component of network security, providing advanced capabilities beyond basic packet filtering. Let’s recap the key points discussed:
- SPI differs from stateless packet filtering by maintaining connection state tables and analyzing packets in the context of those connections. This contextual analysis allows for more precise rule enforcement and enhanced security.
- SPI can block specific applications or protocols, but its primary focus is on inspecting packet headers, maintaining connection state, and enforcing security policies based on contextual information.
- SPI may impact network performance, especially in high-traffic environments, due to the additional processing and resource requirements involved in packet inspection and maintaining connection state tables.
- While SPI is effective against a range of network attacks, it may have limitations when dealing with encrypted traffic. Additional security measures like deep packet inspection may be necessary to complement SPI in inspecting encrypted data.
- Implementing SPI in large-scale networks can present performance scalability, rule complexity, network topology, and resource allocation challenges. Careful planning and optimization are required to ensure its effectiveness.
- While SPI enhances network security, it should be implemented alongside other security measures such as antivirus software, intrusion detection/prevention systems, and security audits/assessments for a comprehensive defense strategy.
In light of these considerations, it is recommended to implement SPI as part of a multi-layered security approach tailored to the specific needs and resources of the network environment.
Organizations can strengthen their network defenses and mitigate potential threats by combining SPI with other security measures, regularly updating and optimizing configurations, and conducting thorough security assessments.

Information Security Asia is the go-to website for the latest cybersecurity and tech news in various sectors. Our expert writers provide insights and analysis that you can trust, so you can stay ahead of the curve and protect your business. Whether you are a small business, an enterprise or even a government agency, we have the latest updates and advice for all aspects of cybersecurity.