What is User Management?
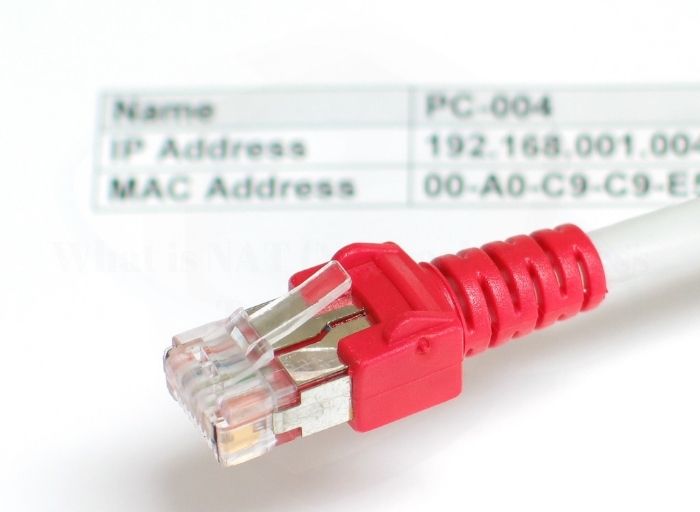
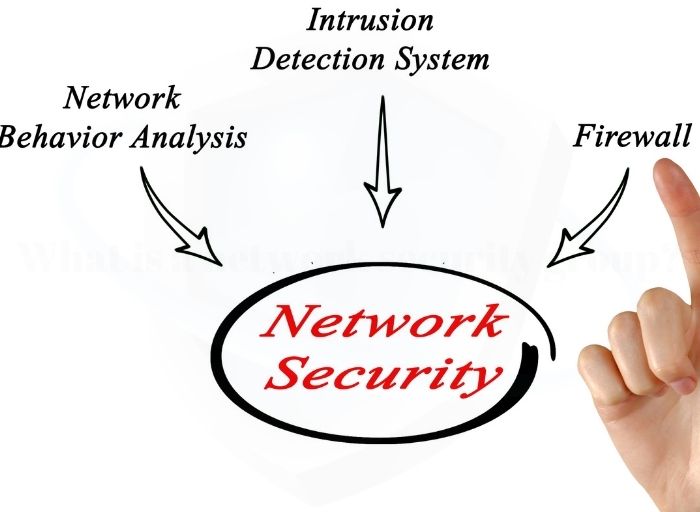
User management is an important task of the administrator. He or she sets up users and user IDs and assigns or revokes access authorizations for IT systems or applications. User administration can be performed directly locally in the system concerned or via an externally connected, centralized database solution. In today’s digital age, user management plays … Read more